Utilizing a combination of automated and manual processes, Business System Solutions engineers will build a business-specific ETL Tool & Data Integration system in which Endpoint Manager data is decoded, translated, parsed, processed, de-duplicated, cleaned, and stored in a relational format. In this format the data is now optimized for reportability, performance, and archiving purposes. The Extract process creates separate objects for each Endpoint Manager analysis exposing all the corresponding individual properties as one record for each system. Denormalizing the data allows for more optimal database performance, while providing end users an intuitive data structure to better understand and manipulate the information presented.
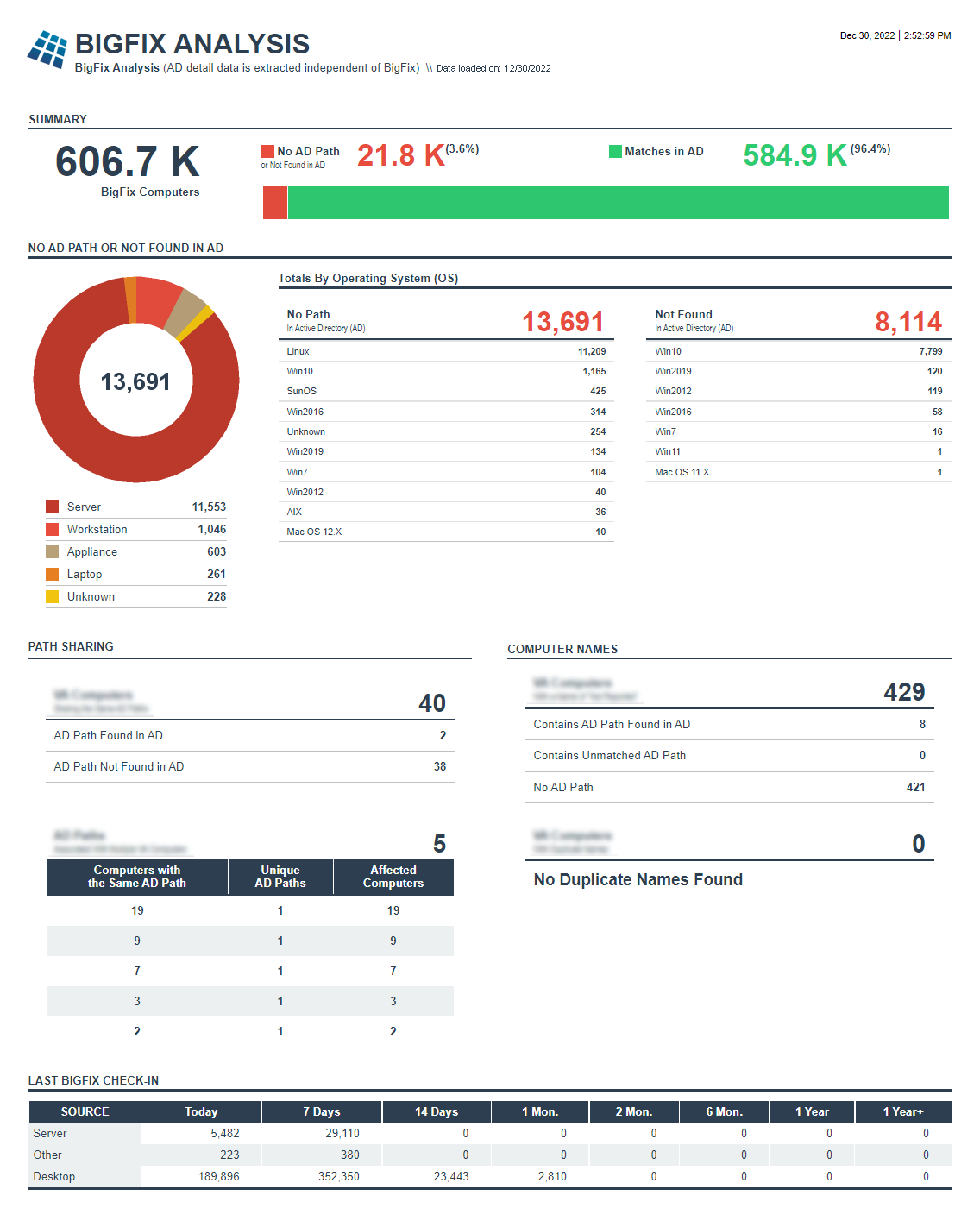
BigFix Analysis Report
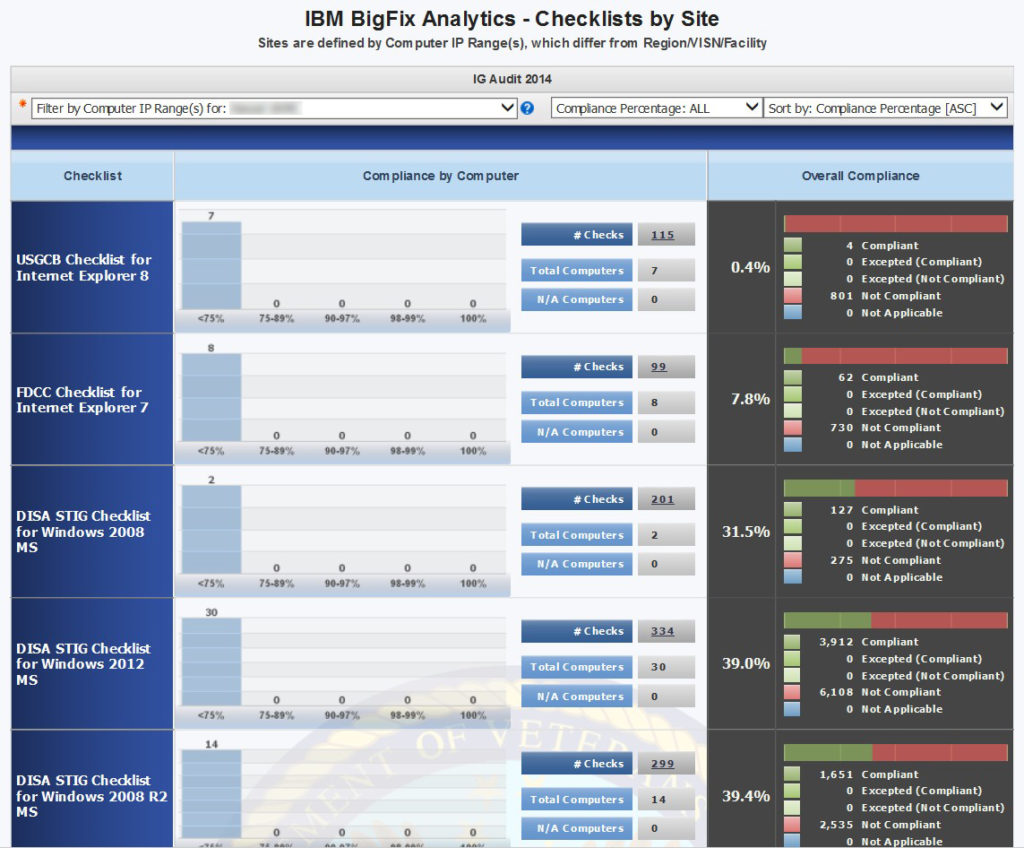
Site Checklist Report
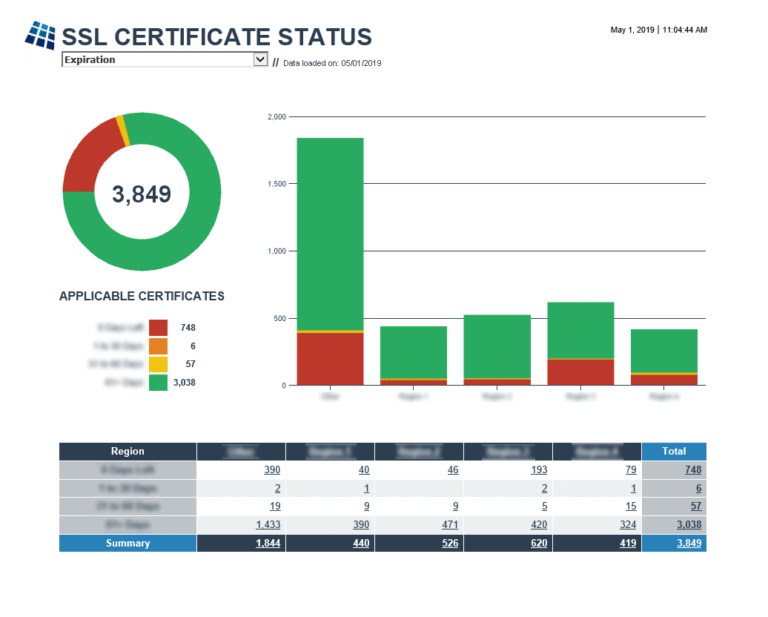
SSL Certificate Status Report
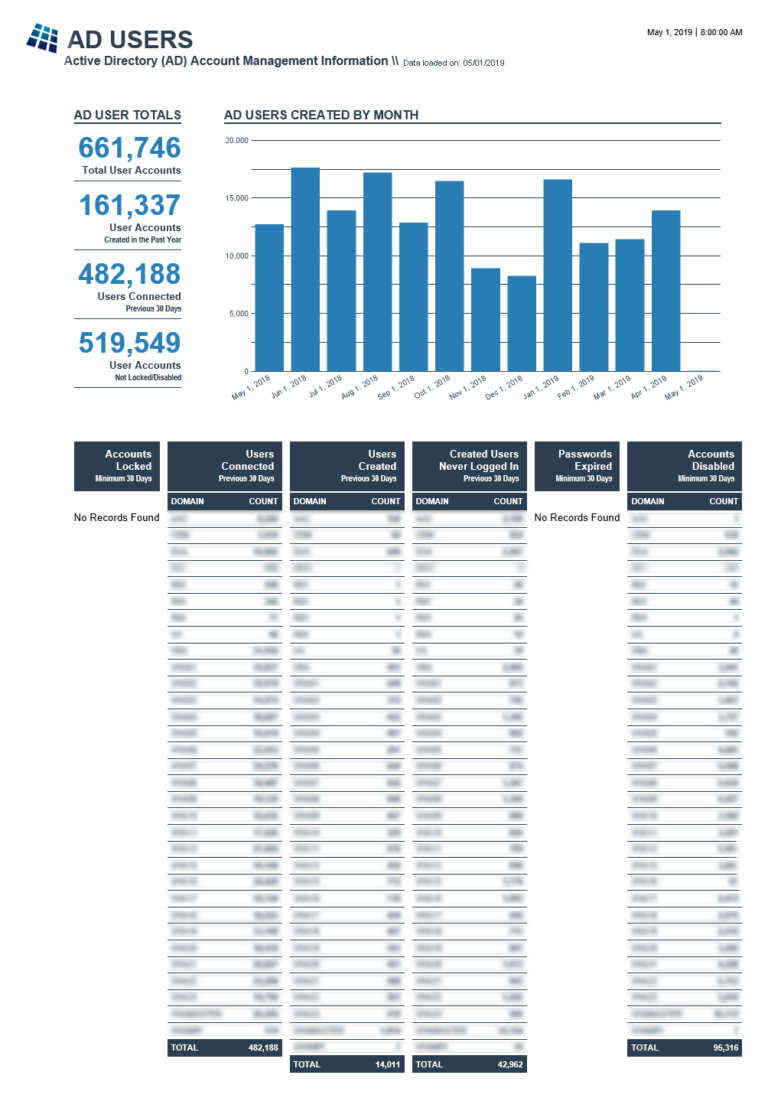
AD Users Report
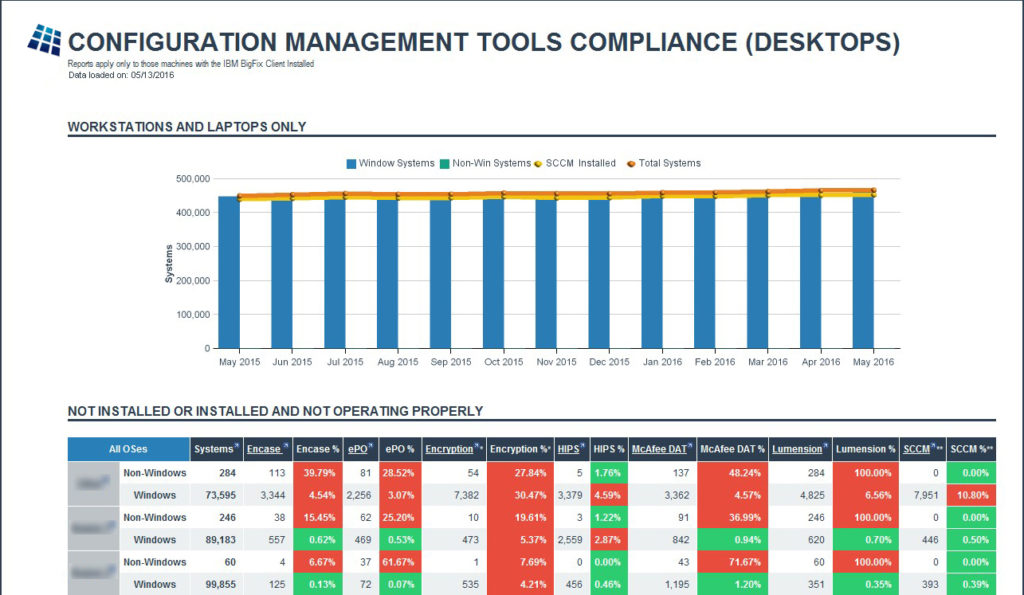
Config. Mgmt. Compliance Report
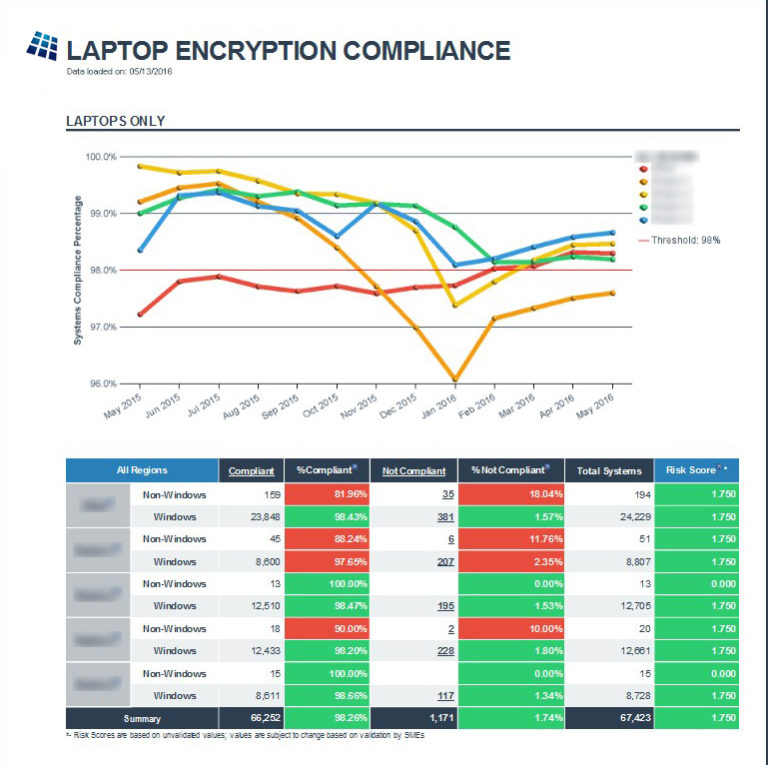
Encryption Compliance Report
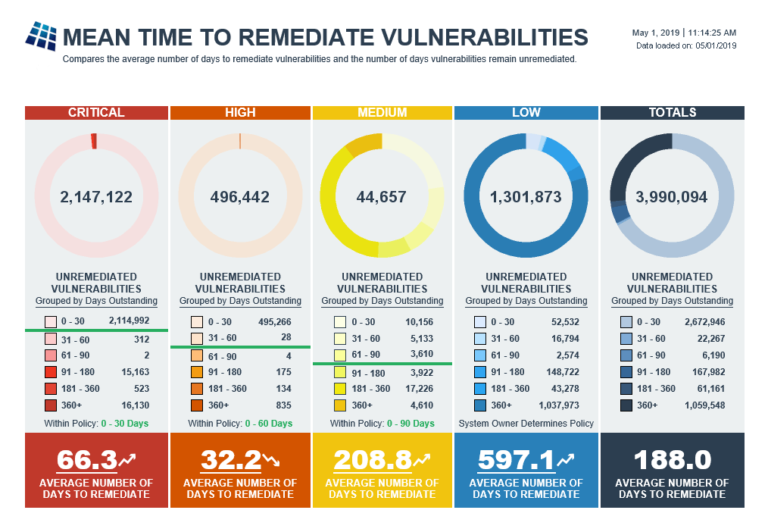
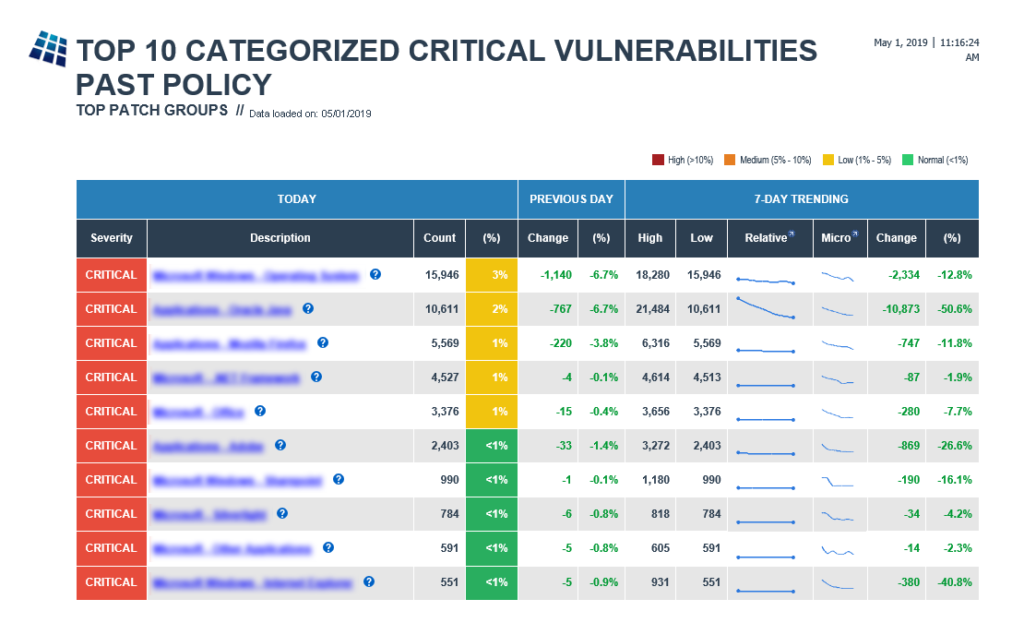
Vulnerability Remediation Report
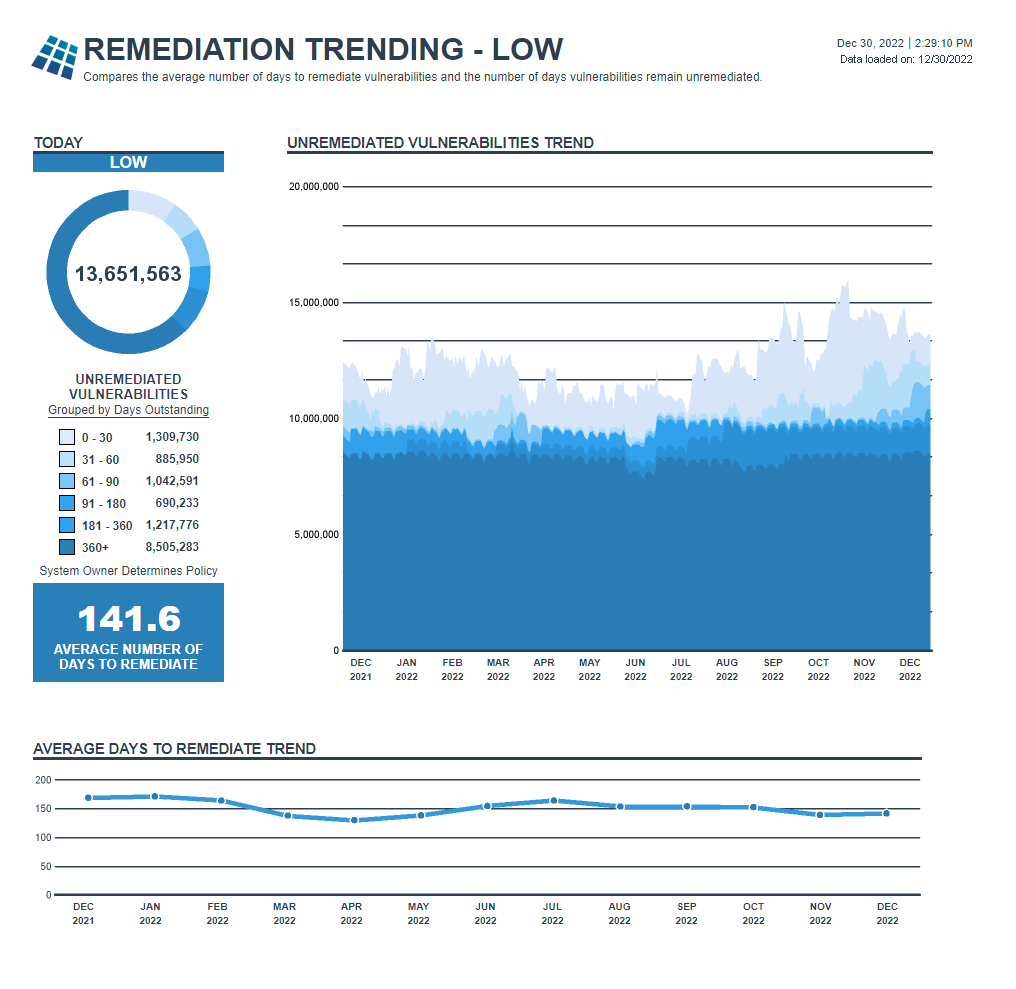
Remediation Trending Report
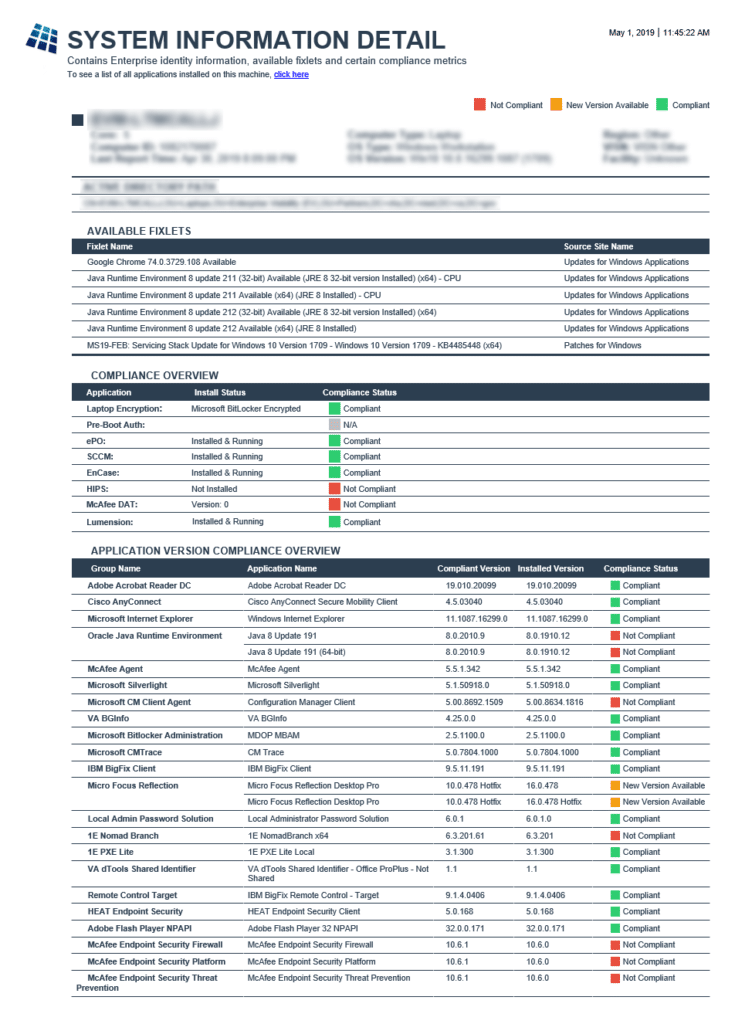
System Information Detail Report
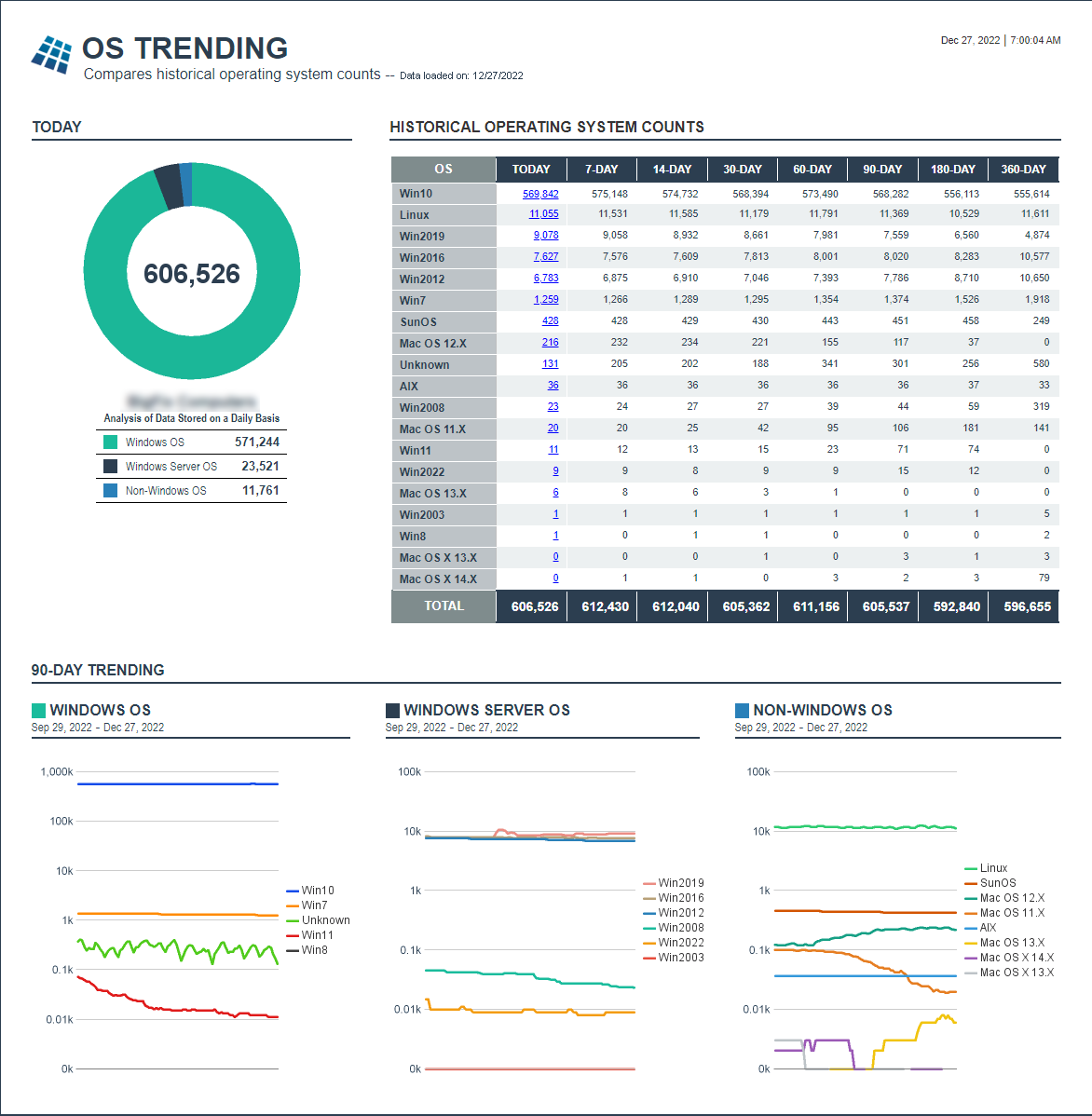
OS Trending Report
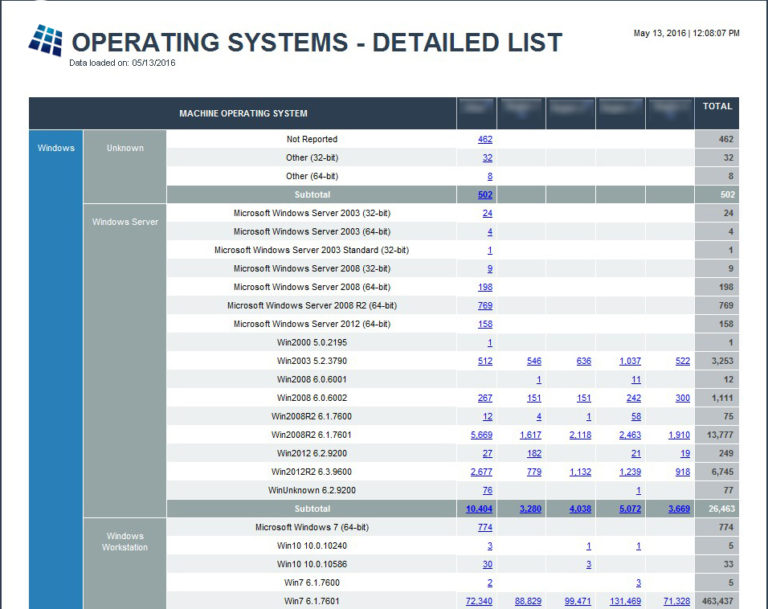
OS Detail Report
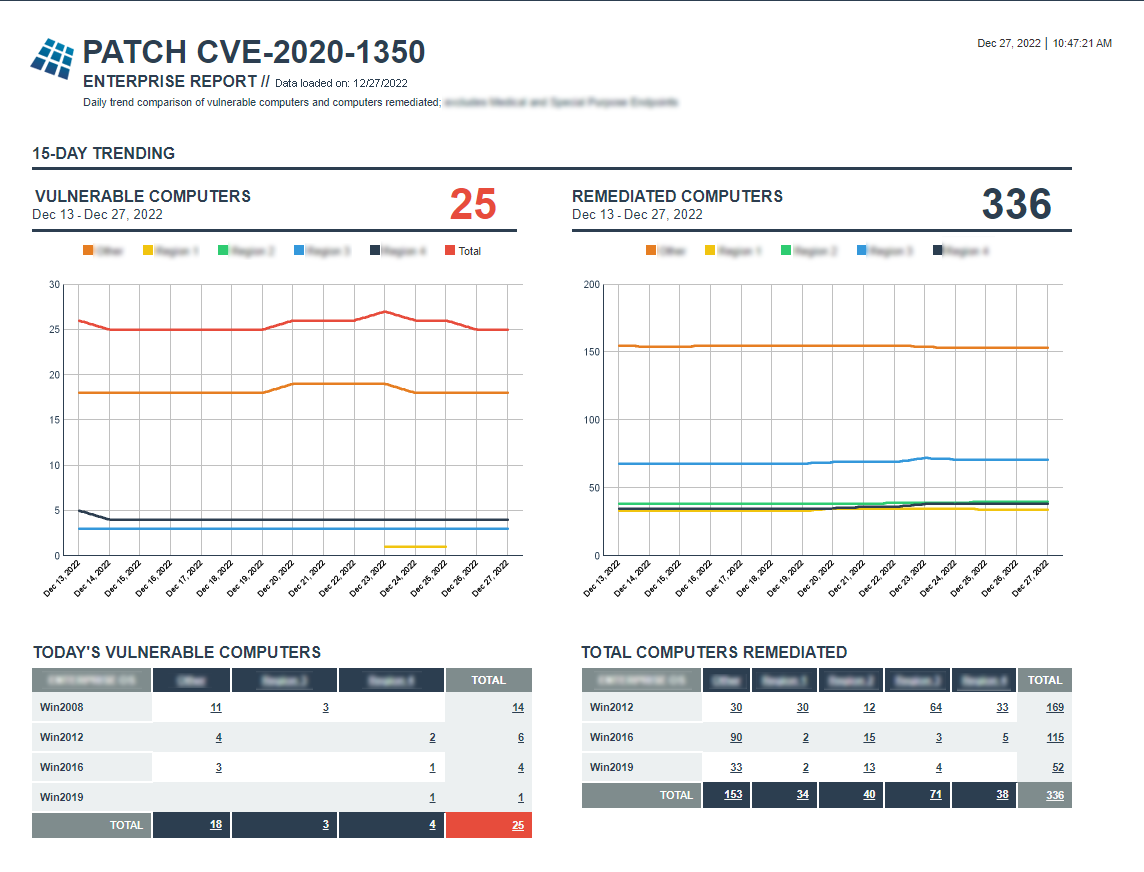
Patch Report
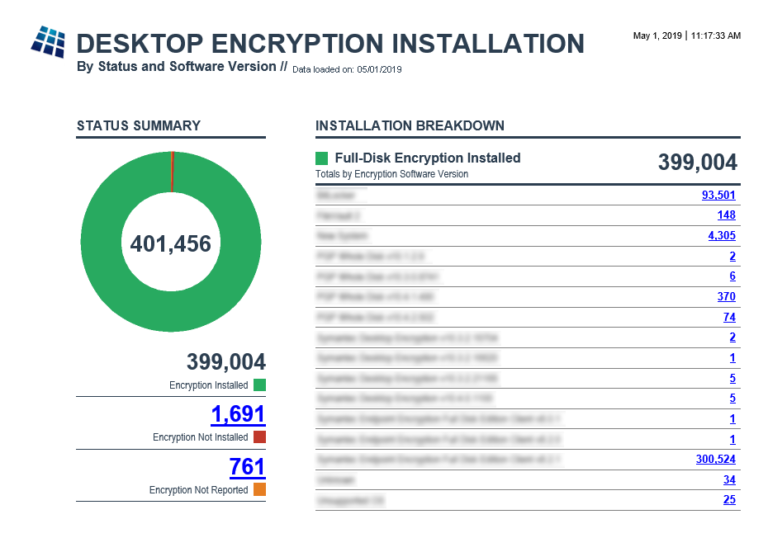
Desktop Encryption Install Report